My Phone Was Hacked. How Do I Fix It?

Updated:

Want to know how to fix a hacked cell phone? Then you’ve come to the right place. This article explains the steps you must take if you suspect your device has been hacked.
We’ll also show you proactive steps you can take to protect your Android or iPhone in the future.
What to Do If Your Phone Is Hacked
Whether using an Android device or an iPhone, falling victim to a hack can be an upsetting experience.
Yet, amidst the initial panic, acting swiftly and decisively is crucial. In the following sections, we’ll outline actionable steps and fixes to help you regain control, secure your device, and prevent further unauthorized access.
Let’s dive in and explore what to do if your phone is hacked.
How to fix a hacked Android phone

1. Disconnect from networks
Most Android malware requires access to the Internet to send your data to a third-party or receive instructions of how to behave on your device.
If your phone is hacked, the first thing you should do is turn off Wi-Fi and mobile data to prevent further unauthorized access or transfer of data.
Putting your phone into Airplane Mode is the quickest and easiest way to do this.
💡Pro-tip: Never use public Wi-Fi networks when accessing your online accounts like your bank accounts. Hackers can gain access to these networks and steal your information.
2. Change passwords
If someone has hacked your phone, they may have extracted any passwords saved to your device or captured them in real-time using a keylogger.
It’s therefore a good idea to change all passwords starting with your Google Account and then passwords for other critical accounts like banking and email from a different, secure device.
3. Find and remove unknown or suspicious apps
If you notice any apps that look out of place or you don’t recognize, it might indicate a spyware infection on your phone.
We advise removing any apps that appear unfamiliar or raise your suspicion. If you come across such an app, follow these steps:
Step 1: Switch to safe mode
- Press and hold down the power button on your device until the power menu pops up.
- Now, press and hold the Power off option listed in the menu.
- A message will show up asking whether you want to reboot into Safe Mode. Hit OK.
- Your device will restart, and Safe Mode will be displayed on the screen’s bottom left or right corner.
- In Safe Mode, all third-party apps are disabled and only system apps are allowed to run. This is useful for troubleshooting as it helps identify whether a third-party app is causing problems on your device.
Step 2: Delete suspicious apps
- Navigate to Settings > Apps or Manage Apps.
- Scroll through the list to identify any unfamiliar or dubious-looking apps. Remove any app that isn’t needed or you don’t recall installing.
- If you find a suspicious app, tap Uninstall.
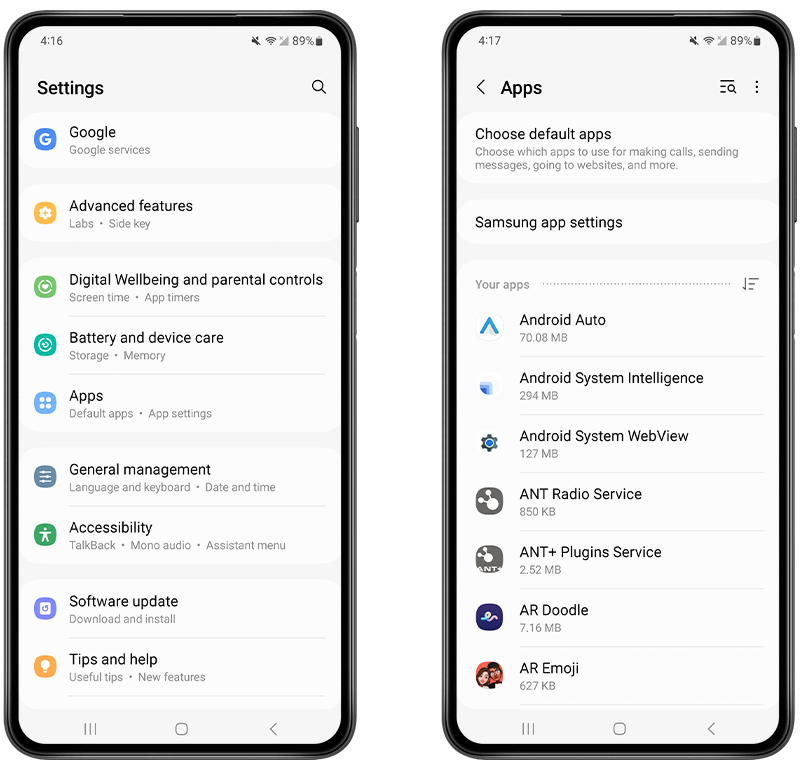
Fig 1: Uninstalling a suspicious app on Android.
- If the Uninstall button is not active (grayed out), it may indicate that the app has device administrator privileges. Malicious apps sometimes obtain these privileges to prevent deletion. Go to Settings > Security & Privacy > Device Admin app.
- Once on the Device Administrators screen, find the malicious app.
- Turn off administrator privileges for the suspicious app by unchecking the box next to its name.
- Return to the previous screen and uninstall the malicious app.
- Restart your phone.
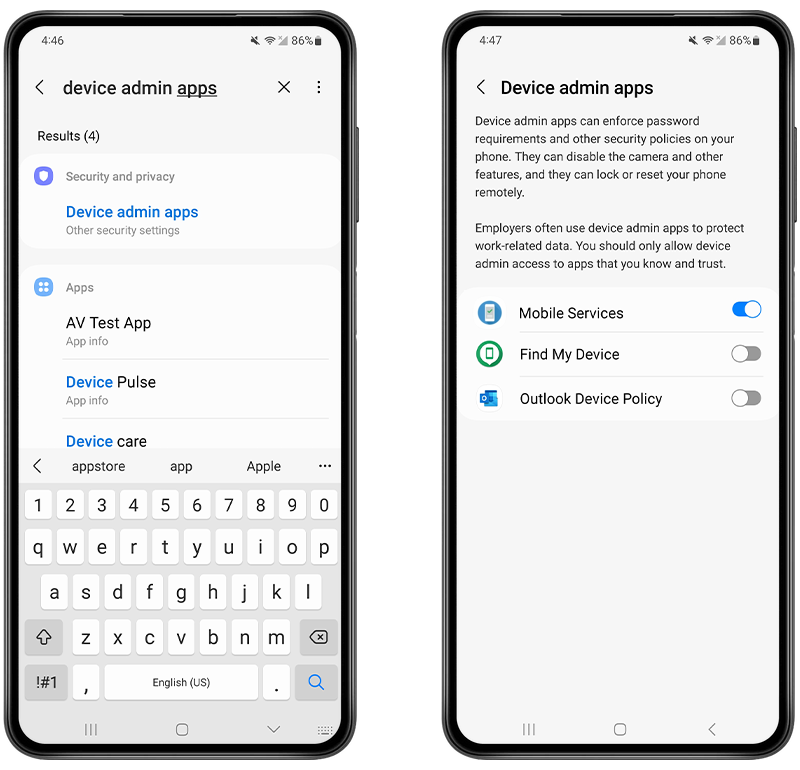
Fig 2: Removing a Device Admin app on Android.
4. Run an antivirus scan
One of the best ways to fix a hacked Android phone is to install a good antivirus app such as Certo Mobile Security. This free app will allow you to perform a full scan of your Android device, discover any installed spyware, and give you the option to remove it with a tap of a button
The app will also check the configuration of your device and highlight any settings that could make your phone vulnerable to attacks.
Here’s how to fix a hacked Android device with Certo:
- Install Certo Mobile Security.
- Open the app and tap Scan.
- Wait for the scan to complete.
- Tap Remove next to any threats found.

Fig 3: Fixing a hacked Android phone with Certo Mobile Security
5. Review app permissions
Another way to secure your device is to review and modify app permissions. This means ensuring that each app only has access to the functions it genuinely needs.
For instance, be cautious of apps that can access your camera or track your location. By monitoring which apps have such permissions, you can quickly identify and remove any suspicious apps pretending to be trustworthy.
Here’s a guide to checking and modifying your app permissions (note that the exact steps might vary depending on your device):
- Open the Settings app.
- Tap Privacy.
- Tap Permission manager.
- Tap each permission (e.g., camera, location) to check which apps have access.
- If you find any suspicious apps with permissions you haven’t granted, tap Uninstall to remove them from your device.
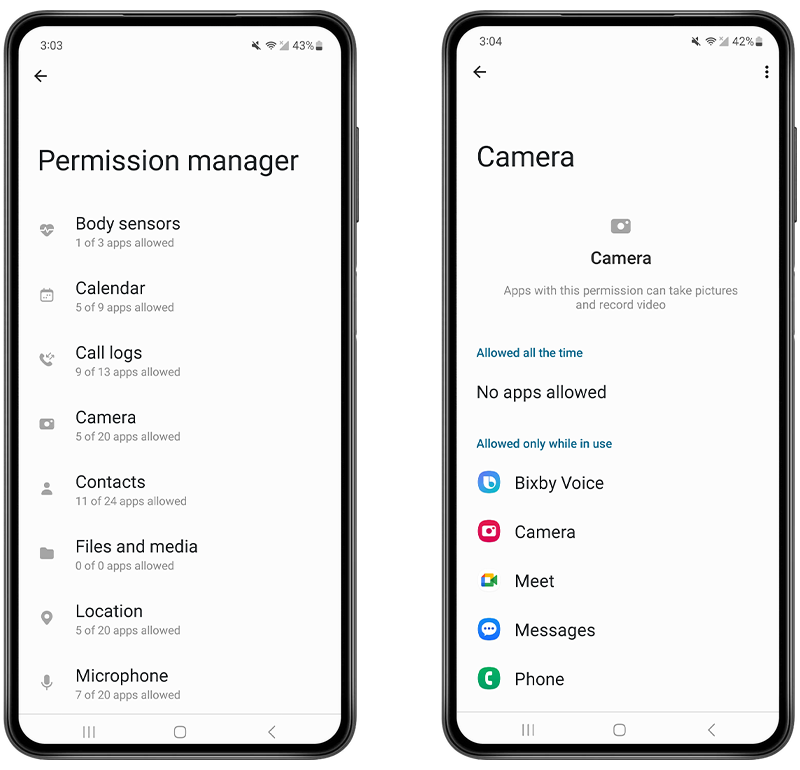
Fig 4: Checking which apps have access to your camera on Android.
6. Update your software
Ensure that your phone’s operating system and apps are fully up to date to protect against known vulnerabilities.
Here’s how to update the operating system on Android:
- Go to Settings > Software update or System update (this might vary depending on the device).
- Tap on Download and install if any updates are available.
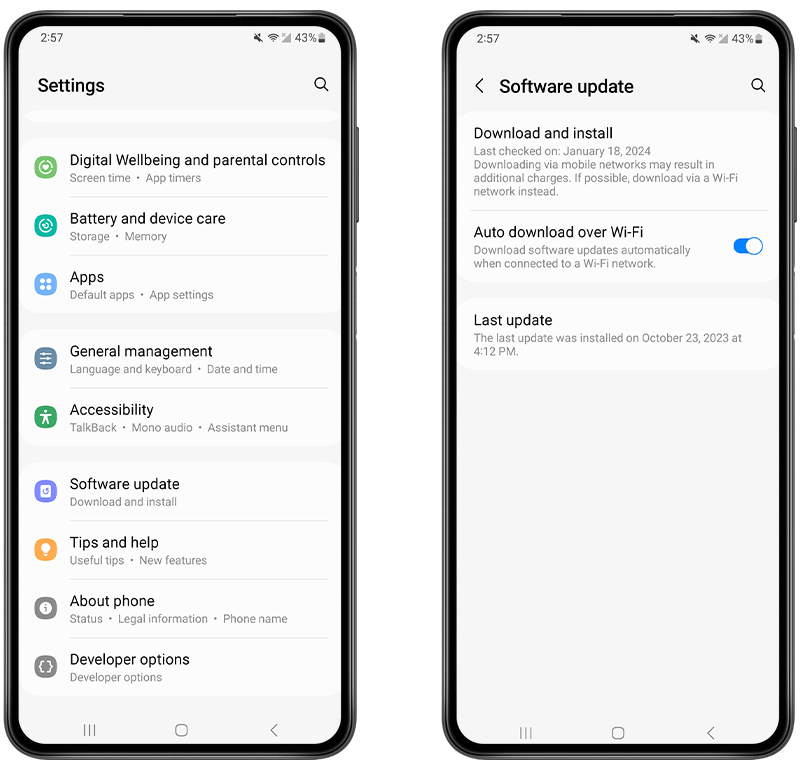
Fig 5: Updating Android OS.
7. If necessary, perform a factory reset
It’s also possible to fix a hacked phone by performing a factory reset, which wipes all the data and installed apps from your phone to return it to its original state.
This option is a last resort and should only be carried out after you have backed up all your important data (photos, music, contacts, etc.) via cloud storage or an external device.
How to do a factory reset for Android
- Navigate to Settings > System (this might vary depending on your device).
- Tap Reset Options.
- Tap Factory Data Reset, and tap again to confirm.
- Depending on your security settings, you may need to enter your PIN or password to authorize the operation.
How to protect your Android phone from hacking in the future
- The best way to protect your Android device is to use a security app such as Certo Mobile Security. This will allow you to perform regular scans to stay on top of any potential threats to your device.
- Never root your device. This will make it much easier for hackers to access your phone and steal your data.
- Never install apps from outside the official Google Play Store. This increases your chance of accidentally downloading and installing malicious software.
- Use a strong passcode or pattern to lock your phone and use biometrics if available.
- Keep your phone’s operating system and apps up to date to prevent hackers from gaining access.
- Make sure specific system settings are correct, including:
- Play Protect set to enabled.
- Developer Options set to disabled.
- Allow Apps from Unknown Sources set to disabled.
How to fix a hacked iPhone

You have a few options to fix a hacked iPhone or any other iOS device.
1. Restart your device
It sounds simple, but restarting your iPhone can help stop malicious processes running in the background and can even remove some exploits entirely.
To restart, hold down the side button and either of the volume buttons until the power off slider appears.
Once the device is off, hold the side button again to turn it back on.
2. Update the device’s operating system
If you suspect your iPhone has been hacked, it’s a good idea to ensure you are running the latest version of iOS. Hackers often exploit security vulnerabilities from out-of-date operating systems to access people’s phones, so don’t make it easy for them.
Updating iOS will often stop any installed malware from functioning, so it can be a quickly way to fix a hacked iPhone:
- Unlock your iPhone and go to the Settings app.
- Scroll down and tap on General.
- Now tap on Software Update. Your iPhone will check for updates.
- If an update is available, tap on Download and Install.
- If prompted, enter your passcode.
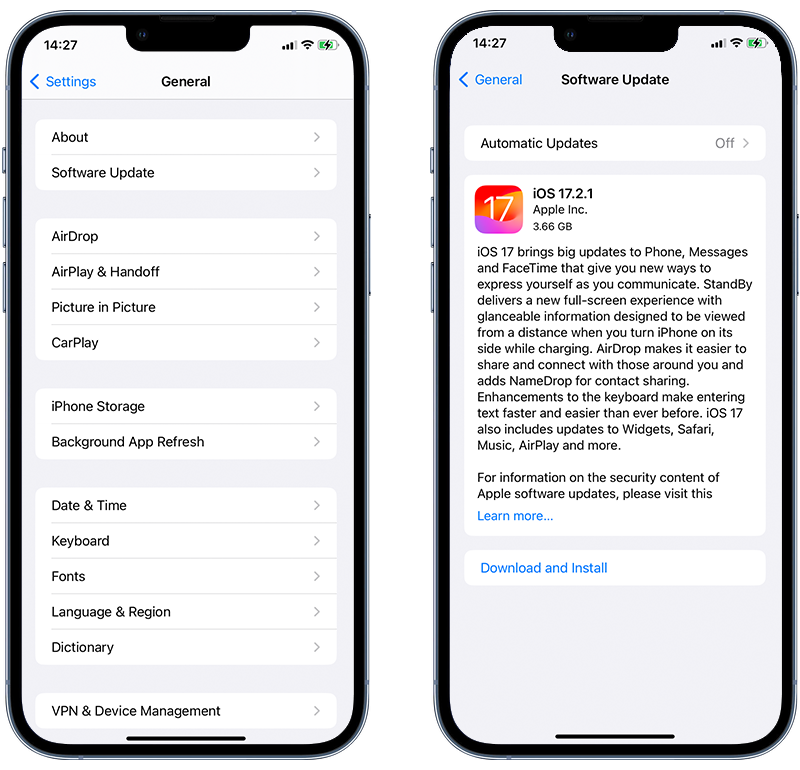
Fig 6. Performing an iOS update on iPhone.
💡 Pro-tip: To have your iPhone update automatically in the future, go to Settings > General > Software Update > Automatic Updates, then turn on Download iOS updates or Install iOS updates.
3. Run an antivirus scan
One of the best ways to fix your hacked iPhone is by using an antivirus tool like Certo AntiSpy. This software can do a full scan of your device to help you determine whether you’ve been the victim of a hack and help you safely remove any malware or spyware.
Here’s how to identify threats with Certo AntiSpy:
- Download Certo AntiSpy on your computer.
- Plug in your phone using a USB cable.
- Click Scan.
- Click Remove on any threats that are discovered.
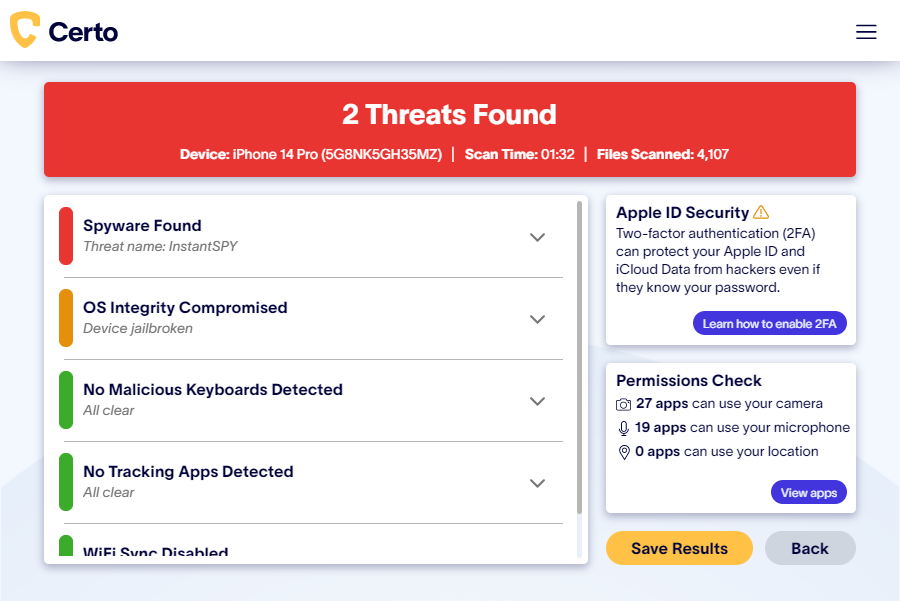
Fig 7. Detect spyware on an iPhone with Certo AntiSpy.
4. Change your Apple ID password
Sometimes hackers may steal data from an iPhone indirectly, by gaining unauthorized access to the victim’s iCloud account and downloading a copy of synced data. This can include things like photos, messages, calendar entries and private notes.
If you can access your account, immediately change your Apple ID password on your iOS device or browser. Here’s what you need to do:
Using a web browser:
- Go to the Apple ID account page and log into your account.
- In the Sign-In and Security section, click Password.
- Follow the on-screen instructions to reset your password. Depending on your account settings, you might be given different options, like answering security questions, getting an email to reset the password, or using two-factor authentication.
Using an Apple device:
- Go to the Settings app.
- Tap on your name at the top, which opens the Apple ID screen.
- Tap on Sign-In & Security.
- Tap Change Password. If you’re signed in to iCloud and have a passcode set up for your device, you’ll be prompted to enter it.
- Enter your new password and confirm it.

Fig 8: Changing Apple ID password on an iPhone.
It’s important to note that your Apple ID password should differ from those of your other online accounts. This is standard good practice to maximize your Apple ID security. Also, always use a passcode lock for your device and use complex passwords.
5. Check your device list
If your iPhone or Apple ID has been hacked, checking the devices connected to your Apple ID is essential.
Cybercriminals might add their devices to your account, which allows them to access your information and make changes without your knowledge.
Here’s how to see which devices are linked to your Apple ID:
- Open the Settings app.
- Tap on your name at the top to access Apple ID settings.
- Scroll down to the list of Apple ID devices associated with your Apple ID.
- Tap on any device name to see more details, like the device model, OS version, and serial number. If needed, you can then remove a device from this list.
6. Do a factory reset
Restoring your device to its original state is another possible way to fix a hacked iPhone, but it is a last resort.
Choosing this option will wipe all of your data from your phone, so you’ll need to back it up first before you do it, either to iTunes, Finder, or iCloud.
Here’s how to do a factory reset:
- On your iPhone, open the Settings app.
- Scroll down and tap on General.
- Scroll to the bottom and tap on Transfer or Reset iPhone.
- Select Erase All Content and Settings.
- You may be asked to enter your passcode or Apple ID password to confirm.
- A warning will appear, informing you that this action will erase all data from your device.
- Confirm that you want to proceed by tapping Erase iPhone.
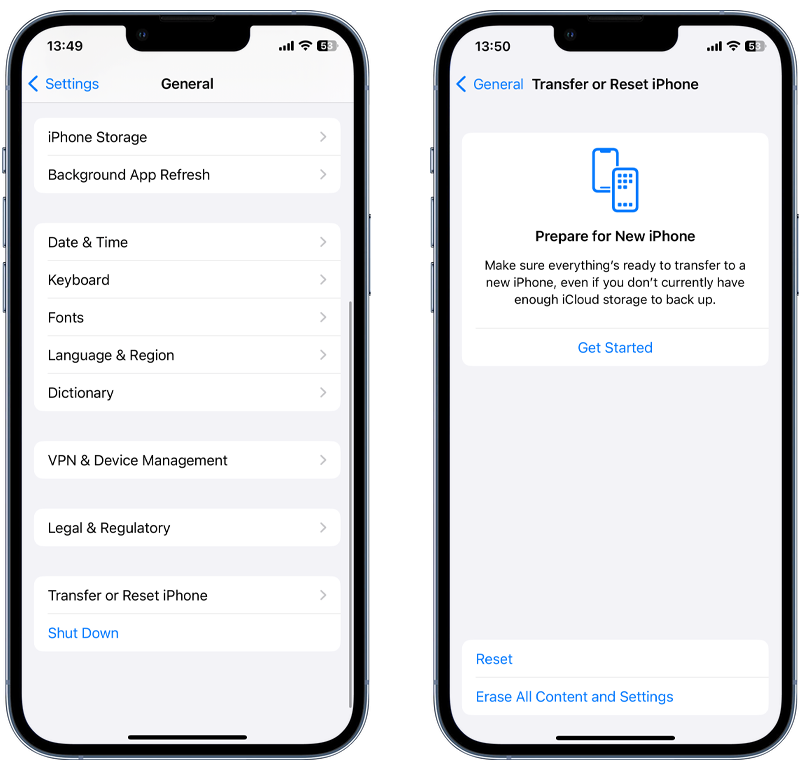
Fig 9: Performing a factory reset on iPhone.
How to Protect Your iPhone from Hacking in the Future
Once you’ve fixed your hacked iPhone, you should take steps to prevent it from being hacked again in the future:
- Run regular malware scans, with a tool such as Certo AntiSpy.
- Turn on automatic updates to ensure your iOS version is always up to date.
- Never jailbreak your device.
- Never download apps from outside the official App Store.
- Always use a strong passcode to unlock your phone.
- Keep your apps up to date.
- Use two-factor authentication with your Apple ID—some hackers may target your iCloud account if your device is set to sync to the cloud.
- Educate yourself on how to recognize suspicious activity to prevent future hacks. More on this below!
Phone Hacking Explained
Now that you know how to fix a hacked phone, it might help to understand the methods that underlie phone hacking and how to identify telltale signs that your device might be compromised. This will help you watch out for them in the future.
Phone hacking encompasses various methods that cybercriminals employ to gain unauthorized access to your personal data and device functionalities.
Recognizing the red flags early can be the key to swift intervention and optimized security. In this section, we’ll explore the warning signs you should look out for.
What is phone hacking?
We use our phones every single day. They hold a wealth of personal data that would be disastrous if it were to fall into the wrong hands—for example, your address, bank details, personal text messages, photos, and more.
Hackers can use this information to blackmail you, impersonate you online, or steal your data and money.
Simply put, a hack is when a third party (it could be anyone) installs malicious software onto your device to steal data, monitor your activity, or track your location.
Nowadays, a hacker doesn’t have to be a computer specialist—they can simply install commercially available spyware that can be bought online for as little as $30.
Think your phone is hacked?
Run a spyware check on your cell phone today with our easy-to-use apps for iPhone or Android.
How do I know if my phone has been hacked?
Look out for a few tell-tale signs of a hacked phone. Although some of these signs aren’t a guarantee of a compromised device, it’s important to be aware of them and to take action if necessary.
⚠️ High data usage
If you notice that you’re reaching—or exceeding—your phone’s data limits and you’re not sure why, this could be a sign of phone hacking. Hackers often install malicious apps on your phone, which use lots of data to send your information to their own device.
Of course, there could be other explanations—for example, if you’re playing lots of games or watching videos on your phone while using mobile data—but it’s still something to look out for.
Low internal storage space could also be an indicator of a hacked phone, since spyware can take up lots of room.
⚠️ Suspicious apps
Chances are that you have lots of apps installed on your phone—some that you use daily and others that you never use at all. However, it’s important to be vigilant and look out for any unknown apps that appear on your phone.
Hackers only need physical access to your phone for a few minutes to install spyware, which grants them access to all your personal information.
Sometimes you’ll be able to identify the spyware on your phone in the form of an app you don’t remember installing. Be particularly wary of unknown or unrecognized apps with access to your location, camera, or microphone, since this is a common characteristic of spyware apps.
As well as unfamiliar apps, look out for unnecessary files on your phone. Spyware often hides in places where you’re unlikely to notice it, such as hidden files or folders.
⚠️ Battery draining quickly
If your battery suddenly drains much quicker than usual, it could be a sign of a hacked phone. Since malicious software uses lots of data and processing energy to send information to hackers, your phone might be working harder than usual to keep up.
It’s important to note that although this is a possible sign of phone hacking, it’s not the only explanation. Phone batteries naturally degrade over time, so if your phone is a few years old, this could be the reason.
Key Takeaways
Phone hacking is a real threat in today’s hyper-connected world. To protect yourself from threats, you should take steps to ensure your phone’s security.
- Install Certo Mobile Security for Android or Certo AntiSpy for iPhone to quickly identify and remove malware or hackers from your phone.
- Look out for suspicious apps on your phone, and delete them immediately if you find any.
- Improve your phone’s security by choosing strong passwords that would be difficult for anyone to guess. Change them regularly, and consider using a password manager to help. We recommend NordPass.
- Use two-factor authentication for an extra layer of protection against hackers.