How To Tell If Someone Is Accessing Your iPhone Remotely

Published:

Many iPhone users don’t worry about security because they think Apple devices are completely safe.
This is true to an extent. Apple’s closed development and regular operating system updates make iPhones more secure than Android phones.
But iPhones can still be hacked. For example, we made the news earlier this year after highlighting a new iPhone security loophole that cyberstalkers were actively exploiting.
If cybercriminals do hack your iPhone, they could gain access to your personal data including emails, messages, photos, and sensitive information like credit card numbers and passwords.
If you’re an iPhone user, it’s important to know how to tell if someone is accessing your device remotely.
This article explains how you can prevent hackers from remotely accessing your iPhone. We’ll also explain how you can tell when someone has access to your device and what you can do to stop them.
💡 TLDR: How to tell if someone is accessing your iPhone remotely
Don’t have time to read the full article? No problem.
Here are the four main ways hackers might be accessing your phone remotely, with the solutions:
💡 There is spyware on your phone: Use a good anti-spyware app.
💡 Someone has hacked your iCloud: Change your password and remove unknown devices from your Apple ID.
💡 Someone is tracking you using family sharing: Remove unknown users from family sharing.
💡 Someone has set up an unknown linked device on WhatsApp: Go into your linked devices and remove the device.
Four Ways Someone Can Access Your iPhone Remotely and How to Stop Them

There are four main ways that someone could remotely access your iPhone.
1. Installing spyware on your iPhone
Spyware is a type of malware used to illegally collect a victim’s personal data and track their activity.
It gives cybercriminals remote access to things like the victim’s location, call logs, text messages, and online activity. They can even see what the person is typing and listen to their calls.
There are three main ways for spyware to end up on your iPhone:
- The hacker gains physical access to your phone and installs malicious software.
- The hacker tricks you into downloading it yourself. This could be done by sending you a phishing email made to look like it comes from a trusted company. These scam emails often ask you to click on a link—when you do, it automatically downloads spyware without you knowing.
- You download a malicious app from the App Store. Cybercriminals upload some apps to the App Store so they can spy on you and steal your data. However, Apple has strict developer verification requirements, so this kind of attack is rare.
Signs that you have spyware on your iPhone
There are many signs that you may have spyware on your phone. Keep in mind that most of these signs could also be caused by other things, but if you notice several of these signs you should investigate further.
- Your phone is getting hot
- Someone knows details of your private conversations.
- The iPhone battery is running down fast
- Your phone takes longer than usual to shut down
- You discover an app called Cydia on your phone
- Unexplained higher than usual data usage
- You have unfamiliar apps on your phone
How to remove iPhone spyware
There are several ways to remove spyware from your phone. Perform these steps in order:
- Restart your device: Certain types of spyware require a constant connection to their source. Break this connection by restarting yours and they stop working. Easy!
- Update iOS: Spyware often targets vulnerabilities in out-of-date software. By updating iOS you will also likely stop the spyware from working.
- Find the app yourself: Go through your installed apps and folders and try to spot and delete any suspicious-looking apps.
- Use an anti-spyware app: Apps like Certo AntiSpy can be used to quickly and easily scan your device for malicious apps and remove them completely.
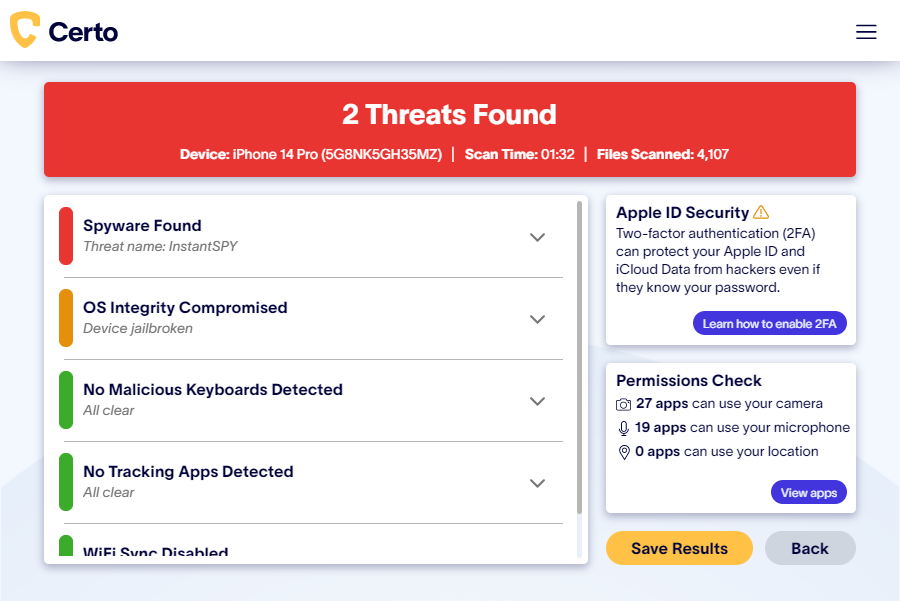
Fig 1: Certo AntiSpy detecting spyware on an iPhone
How to protect your iPhone from spyware
Protecting yourself from spyware is about awareness and proactivity:
- Use anti-spyware like Certo AntiSpy
- Avoid clicking suspicious links
- Avoid suspicious apps, i.e. ones that are slow, glitchy, or look outdated
- Always read reviews before downloading something from the Apple App Store
2. Hacking your iCloud account
If someone hacks your iCloud account, they could see your location, iMessages, call logs, photos, videos and more from anywhere in the world.
However, they can only access the data you have synced from the iPhone to iCloud.
iCloud hacking can be hard to detect and if unnoticed, cyberstalkers could have access to your data for years.
Image by kjpargeter on Freepik
Signs that your iCloud has been hacked:
If your iCloud has been hacked, you’ll notice unusual activity, such as:
- Your Apple ID password doesn’t work
- Your iPhone is mysteriously locked or in Lost Mode
- Unrecognized devices in your iCloud account
- You receive an unexpected login notification
How to remove connected devices from your Apple ID
Here’s how to remove an unrecognized device:
- Open the Settings app on your iOS device
- Tap your name
- Scroll down and tap the device you want to remove
- Tap Remove from Account

How to protect your iCloud from being hacked:
Protecting your iCloud from hackers is relatively easy.
- Change your Apple ID and password regularly
- Turn on two-factor authentication
- Disable iCloud sync on your device
- Turn on Advanced Data Protection for iCloud
3. Tracking you using Family Sharing
Cybercriminals can remotely track your location by adding themselves to your Apple ID’s Family Sharing devices.
To do this, they either need to hack your Apple ID or gain physical access to one of your devices. The ways to protect yourself from this threat are the same as those used to protect your iCloud from being hacked.
How can you tell if someone is tracking you using Family Sharing?
- Open the Settings app on your iOS device
- Tap your name
- Tap Family Sharing
- See if any unrecognized users are shown
How to remove an unrecognized user from Family Sharing
- Open the Settings app on your iOS device
- Tap your name
- Tap Family Sharing
- Tap the user you want to remove
- Tap Remove <name> From Family
4. Setting up a Linked Device with your WhatsApp account
Hackers don’t just target devices; they might also try and spy on the communication apps you use on your iPhone. A good example of this is WhatsApp. You probably use it for things like calls, messages, and sending videos and photos.
WhatsApp is generally secure, as it encrypts data—so only devices that send and receive messages can read them. However, if a hacker gains access to your iPhone they could easily configure WhatsApp to give them remote access to all of your new messages.
Cybercriminals do this by adding themselves to your account as a Linked Device.
Signs that your WhatsApp has been hacked
If your WhatsApp has been hacked, then you’ll probably notice strange activity, like:
- You can see devices you don’t recognize in your Linked Devices
- Your account is sending and receiving messages you don’t recognize
- Messages are being marked as read even though you’ve never seen them before
- Your other contacts are receiving strange messages or calls from your account
- You receive a notification saying that someone has tried to assign a device to your account
How to find out if there are unknown Linked Devices on your WhatsApp
- Open WhatsApp
- Open the Settings menu
- Choose Linked Devices
- Check the list for devices that you don’t recognize
- Tap the unrecognized device and select Log Out

How to protect your WhatsApp from being hacked
Protecting your WhatsApp account involves typical online security measures.
- Use a strong passcode for your device
- Make sure two-factor authentication is turned on
- Never share your verification code with anyone
- Keep your phone with you at all times
Protect Your iPhone from Cybercriminals with Certo

Three of the techniques for gaining remote access to your iPhone that we have listed involve physically accessing your device.
You can easily protect yourself from these by using secure passwords, two-factor authentication, and keeping your phone with you at all times.
However, protecting yourself from spyware isn’t as straightforward. For this, we recommend you use software like Certo AntiSpy to quickly and easily find out if you have been hacked remotely and remove threats quickly and easily.
Here are some of the benefits:
- Quick and easy: Find out if you have been hacked, compromised, or bugged in one click.
- Detect spyware: Find out if you have spyware installed on your iPhone and whether someone is reading your messages and listening to your calls.
- Detect jailbreaks: Detect the jailbreaking software that allows hackers to remove device restrictions and install spyware.
- Detect tracking: See which apps are tracking your location or accessing your microphone or camera.
- Remove threats: Safely remove threats or view simple instructions on how to do this yourself.

