How to Detect Spyware on Android

Updated:

Spyware is a form of malicious software designed to infiltrate and gather sensitive data from a user’s device.
The data that can potentially be stolen is wide-ranging, from personal photographs and private messages to critical account credentials. The unsettling reality? Installing spyware on Android devices is alarmingly simple.
To many, it is surprising how easy it is to embed spyware in an Android phone. Malicious software can be installed in minutes, with some tools available for as little as $29.
Unlike iOS, Android attacks don’t require complex software skills, and it can be as simple as downloading an app onto a device. Android phones are more open than Apple phones, which makes them easier targets.
However, just because your device can be targeted doesn’t mean you can’t protect it. In this article, we’ll teach you how to find spyware on your phone, get rid of it, and understand it better. Plus, we’ll share tips on how to stay safe in the future.
Free anti-spyware for Android
Download Certo Mobile Security from the Play Store now to find and remove spyware from your device.
How to Detect Spyware on an Android Phone
It’s vital to ensure the security of our Android phones, especially with the rise in spyware attacks that we saw in 2023.
As mentioned above, spyware secretly tracks and collects information from your device. If you’re an Android user, understanding how to spot signs of this malicious software is key to keeping your data safe.
At a glance: The signs of a malware infection on your Android phone
Here are some of the key signs you should out look for that could mean spyware has been installed on your Android device:
🚩 Poor battery life
🚩 Battery overheating
🚩 Increased data usage
🚩 Apps slow to load
🚩 Strange phone behavior like random pop-ups, unfamiliar apps, and suspicious files in your download manager
We’ll discuss these and more in detail below 👇
1. Is your battery life not as good as it used to be?
While batteries naturally degrade over time, a sudden and significant drop in battery life might suggest the presence of spyware.
Such malicious software runs resource-intensive processes in the background, which increases battery consumption. Spyware could be the culprit if your device’s battery drains quickly with only light usage.
2. Does your phone get hot?
If your phone becomes unusually warm during basic tasks like checking emails or browsing the web, it might indicate extra background processes. Spyware operating in the background can strain the device’s processor, causing it to overheat and this, in turn, leads to inconsistent battery life.
3. Does your data run out too fast?
If you think that your data is running out faster than it should, or you’re just generally using more data than usual, this again could be a sign of hidden spy phone apps installed on your phone that are connecting to the internet and transferring information without your knowledge.
4. Are apps taking too long to load?
If your phone is running slower than normal, then this could mean that you’ve got spyware installed. This sign is usually what people will notice first with their device since it can become increasingly frustrating!
By its very nature, spyware runs multiple processes that can bog down a device’s performance. If apps start slower, tasks lag, or your device frequently freezes or crashes without an apparent reason, it could be burdened by unwanted spyware.
5. Is your Android phone displaying unusual behavior?
Spyware can sometimes interfere with a device’s standard operations. Random pop-ups, unexplained restarts, or odd noises during calls might not just be glitches; they could be signs of a deeper problem.
6. Are you finding suspicious files on your device?
Spyware often creates or downloads files to store the information it gathers. It’s recommended that you regularly browse through your file manager. If you spot unfamiliar or suspicious-looking files, it could indicate your device is compromised.
7. Experiencing random pop-ups?
While some pop-ups can stem from regular internet browsing, an influx of unexpected ads or messages on your screen could result from adware, a subtype of spyware. These pop-ups aren’t just annoying—they can also be harmful if they trick users into downloading more malware or revealing personal information.
8. Finding any unfamiliar apps?
Some malicious spyware disguises itself as legitimate or system apps. If you stumble upon apps you don’t remember installing or seem out of place, it might be worthwhile to investigate these suspicious apps’ origins and functionality.
Some known examples of spyware apps that you should delete immediately are:
🛑 mLite
🛑 Update Service
🛑 Sync Service
🛑 Phone Tool
🛑 Sync Services
9. Difficulty accessing password-protected apps and web pages?
When you try to log in to certain apps or web pages, spyware might redirect you to a spoofed website to capture your login credentials.
This malicious website mimics the real one and then secretly records your details and sends them to unauthorized third parties. Most users remain unaware of this intrusion until adverse consequences surface.
10. Is Google Play Protect disabled?
Google Play Protect is Android’s built-in virus scanner. If you find that yours is turned-off and you did not do this yourself, this could signal that your device is compromised.
Malware often targets and turns off security software to operate without hindrance. By neutralizing the defenses first, malware ensures it can freely manipulate your device.
You can check your Google Play Protect settings as follows:
- Open the Google Play Store app.
- Tap the profile icon at the top right of your screen.
- Tap Play Protect.
- If Play Protect is turned off, this could be a sign that someone has disabled it in order to install a malicious app.

Fig 1. Checking Play Protect on Android.
11. Getting strange and frequent text messages and emails?
Compromised devices often receive deceptive messages to trick users into inadvertently installing spyware. These messages might contain suspicious links, coded symbols, or even masquerade as authentication requests for your social platforms.
Always be cautious about interacting with unfamiliar or unsolicited communications.
12. Are you hearing noises during phone calls?
Hearing unusual static, beeps, or disruptions during phone calls that aren’t due to a weak signal should be cause for concern. Such noises can result from tapped calls or recording processes initiated by spyware.
If you consistently experience such disturbances, it’s worth checking your device for malicious software.
How to Remove Spyware from Your Android Device

Image by Freepik
Identifying spyware on your Android device can be a challenging task to tackle on your own since the solution often isn’t as simple as removing untrustworthy apps.
Therefore, it’s crucial to equip your device with a high-quality malware removal tool and spyware detector to enhance the security of your Android phone.
However, using an antivirus tool is just one part of keeping your device safe—there are additional steps you can take to secure your mobile device.
In the following section, we’ll show you how to remove spyware from your Android device. Through a step-by-step approach, you’ll learn multiple strategies to secure your device and keep it spyware-free.
Detect and destroy spyware
Certo Mobile Security finds and removes hidden spyware fast! Get it for FREE from the Play Store now.
Detect and remove spyware with the Certo Mobile Security App
To detect spyware on an Android phone, consider using a comprehensive anti-spyware and antivirus app like Certo Mobile Security. This app provides:
✅ Device scanning: Quickly scan your Android device for any spyware and, if detected, remove it with a single tap.
✅ Security analysis: Examine various device settings to identify potential vulnerabilities.
✅ Privacy audit: Review which apps have permission to access features like your microphone and camera.
✅ Auto malware scan: Schedule regular spyware checks for hidden spy apps to ensure continuous protection.
✅ Intrusion alarm: Set an alarm to activate if there’s any unauthorized attempt to access or tamper with your device.
✅ Data breach alerts: Check whether your details, such as email addresses and passwords, have been compromised in major security breaches.
How to use Certo to secure your Android device:
- Download and install the free Certo Mobile Security app from the Google Play Store.
- Open the app and select Scan.
- Once the scan finishes, tap Remove next to any detected threats found.
- Always install updates to the app as they introduce new features, which offer users robust protection and peace of mind.

Fig 2. Detecting threats with Certo Mobile Security.
Update your Android operating system
Ensure that your phone’s operating system is up to date. Software updates usually contain security patches that could potentially remove spyware from your Android device and protect against known vulnerabilities.
Here’s how to update your device’s operating system:
- Go to Settings > System > Software update or System update (this might vary depending on the device).
- Tap on Download and install if any system updates are available.
Factory reset if necessary
If all else fails, you can do a factory reset. A factory reset on an Android device will erase all data, including files, settings, and apps. Here’s how to do it:
Step 1: Back up your data
Before you perform a factory reset, it’s crucial to back up your data to prevent losing important information. You can back up your data to Google Drive or an external storage device.
Step 2: Initiate factory reset
- Go to your phone’s settings.
- Scroll down and tap on System (the exact path may vary slightly depending on your device).
- Now tap on Reset or Reset options.
- Select Erase all data (factory reset) or Reset phone.
Step 3: Confirm factory data reset
- You might be asked to enter your device passcode or Google Account password to confirm the action.
- Confirm your decision by selecting Erase Everything, Reset Phone, or any similar option that will initiate the reset.
Step 4: Wait for the reset process to complete
The device will reboot and the process will begin. It may take a few minutes to complete the factory reset.
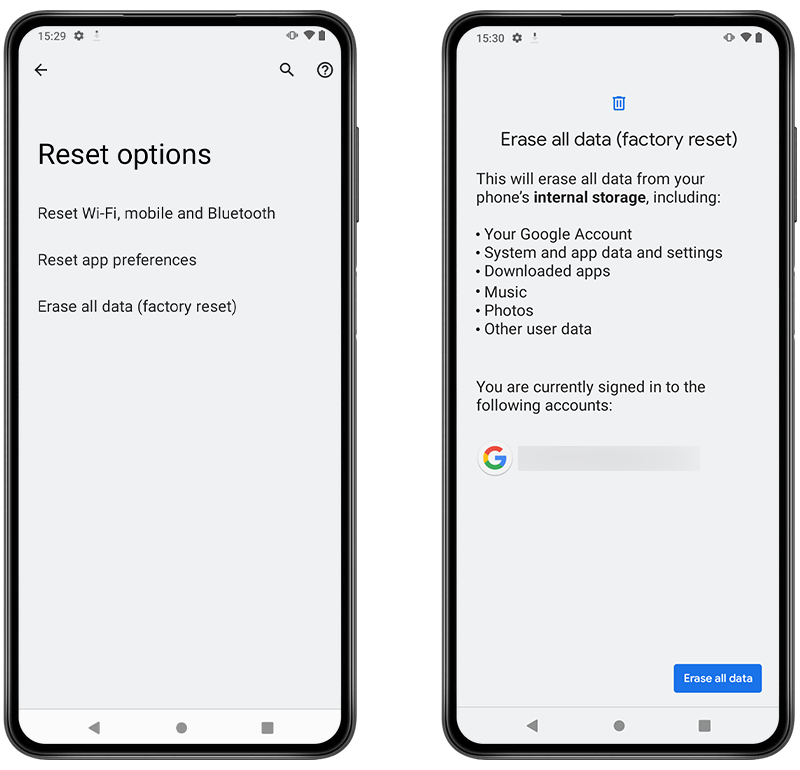
Fig 3. Performing a Factory reset on Android.
Everything You Need to Know about Spyware
Now that you’re familiar with how to detect and remove spyware from your Android device, it’s time to understand this threat more deeply.
Spyware is malicious software that quietly collects information from your device. But it’s not a one-size-fits-all scenario; there are various kinds of spyware, each with its own tactics.
In this section, we’ll break down what spyware is and go through the types you might encounter.
What is spyware?
Spyware is a malicious app or software that can gather a wide range of information, including personal details, private messages, passwords, and browsing habits of unsuspecting Android users.
Cybercriminals, unethical advertisers, or entities interested in gathering information about individuals or organizations often use spyware apps. It typically infiltrates devices through deceptive means such as a phishing attack via email, malicious websites, or bundled with other software.
Once installed, spyware operates in the background, which makes it difficult for users to detect its presence. It’s a serious threat to privacy and security, and it’s advisable to use reputable security software and adopt good digital hygiene practices to prevent spyware infections.
What types of spyware exist for Android?
Educating yourself is one of the best ways to stay safe when it comes to protecting your data and your device against cyberattacks.
There are basic things that you should be aware of when it comes to spyware for Android devices. Perhaps most importantly, you should know what the different types of spyware you need to look out for, are:
1. Consumer spyware
This spyware is usually downloaded from third-party app stores or websites and is often marketed as “Catch a cheating spouse” or “Protect your children” software. Simply put, this is software that an individual could install on your phone in just a matter of minutes if they have physical access to it.
The scariest thing about this type of software is that it could give the perpetrator access to everything on the phone, such as photos, messages, and real-time location tracking, as well as giving them the ability to record phone conversations.
It’s bad enough if someone is using this type of software to spy on a partner/ex-partner, but it’s even worse if someone is using it maliciously in order to gain access to sensitive information. The damage could potentially be life-changing.
2. ‘Family Monitoring’ apps
These types of apps are widely available on the official Google Play Store, as well as on third-party app stores.
They are usually marketed at parents who wish to monitor their child’s device—for example, to track their location when they are out on their own or with friends. These apps allow parents to control their child’s phone as well as block certain apps, etc.
However, much like consumer spyware, these apps are available to anyone and could be installed without the device owners permission and misused as a spy app in order to access data.
3. Malicious/Trojan apps
Spyware apps used by hackers that do not have physical access to your device. They are typically disguised as legitimate apps and distributed via phishing attacks or malicious websites.
Be aware however, some of these apps can also make it onto the official Google Play Store. For example, in August 2019, it was discovered that a radio app that over 8 million users downloaded turned out to be infested with adware and spyware, that infected the victims’ devices and collected their data.
4. Other types of spyware
⚠️ Adware: Displays unwanted advertisements, tracks user activity, and collects personal data for advertising purposes
⚠️ Keyloggers: Records every keystroke on a device to capture passwords, login details, and personal messages.
⚠️ System monitors: Record a wide range of user activities, including emails sent/received, keystrokes, and websites visited, posing a severe threat to privacy.
⚠️ Tracking cookies: Tracks user activity and browsing habits, sometimes used maliciously to collect personal information.
⚠️ Password stealers: Harvests passwords from infected devices to gain unauthorized access to personal accounts and sensitive data.
⚠️ Rootkits: Rootkits provide cybercriminals with administrator-level access (or root access) to the victim’s device to hide malware, which makes it difficult to detect or remove.
⚠️ Information stealers: Designed to steal sensitive information from your device, like financial data or personal identification information.
Each type of spyware poses unique threats and requires different approaches for detection and removal. It’s crucial to stay informed and take preventative measures to protect your device from spyware infections.
💡 Expert Insight: What about more advanced software?
Government-grade spyware can be more difficult to detect. Suppose you suspect that your phone has been infected with Pegasus or a similarly advanced commercial spyware.
In that case, you should take it seriously, as such software can give attackers full access to your device, including emails, messages, calls, and even camera and microphone feeds.
Here's what you should do if you suspect your phone has been infected with Pegasus or similar spyware:
➡️ Switch to airplane mode and disconnect from the internet immediately.
➡️ Stop using the device to prevent further data exposure.
➡️ This kind of malware can be very difficult to detect and remove. Contact an IT security expert or firm that specializes in mobile threat analysis.
➡️ Document suspicious activities for cybersecurity experts and, potentially law enforcement.
➡️ Use a different, secure device to change all critical account passwords.
➡️ Inform close contacts about potential security risks.
➡️ Once you're certain it's safe to do so, ideally with an expert's guidance, back up important data from your device.
➡️ As a last resort, and especially if expert help is not immediately available, consider performing a factory reset of your device.
Tips to Protect Against Future Infections
It’s not always easy to keep yourself safe online, and once you’ve been hacked, it takes a lot of effort to get things completely back to normal. Prevention is always better than cure.
Below, we’ll discuss five quick tips for Android users to help you avoid running into problems with spyware on your Android device:
1. Invest in a robust security system
Antivirus software such as Certo Mobile Security can help protect all your important information from prying eyes and data thieves.
2. Keep your device updated
Whenever a new operating system update is released for your device, make sure that you download and install it. This is extremely important to ensure you get all the latest security updates and features from the OS developers. If your device supports automatic updates then be sure to enable it.
3. Don’t click on suspicious links!
This is one of the biggest problems faced by users of any device connected to the Internet—it’s way too easy to click on links that appear genuine but in reality, are fishing for a way to gain access to your info. If you smell a rat, whether online or in your email inbox, steer clear!
4. Use strong passwords
This should be obvious by now! The stronger your password, the harder it is for a hacker to force entry into your various accounts.
Use a variety of alphanumeric characters and symbols to create your password, and make sure it isn’t anything that could be easily guessed. Some services allow you to generate and store random unique passwords for each of your online accounts, which is a great way to improve your password security.
5. Only install apps from trusted sources
Only download apps from the official Google Play Store if you own an Android phone. Don’t download from third-party suppliers.
Downloading third-party apps doesn’t necessarily mean that your phone will get infected with some form of malware, but the chances are much higher via a third party than via the official app store.
Final Thoughts
The digital age has provided many conveniences, but it has also brought its share of threats. As Android users, our devices are increasingly becoming targets for hackers seeking to gain unauthorized access to our personal information.
Spyware, a silent threat, poses significant risks to our privacy and security. However, knowledge is power. By understanding the nature of spyware, its different types, and the signs of an infected device, users can take proactive steps toward ensuring their safety.
One of the most effective ways to protect against spyware is by equipping your device with reliable security software.
Certo Mobile Security for Android is a comprehensive tool that offers various features to detect and eliminate spyware while ensuring continuous protection. We can keep our information safe by being vigilant, regularly updating our devices, and using strong security tools.
Cover Image by Freepik