Can Someone Hack My iPhone?

Updated:

We keep some of our most personal and valued information on our phones, including photos, videos and data we don’t want to be lost or stolen. Technology has given us so many new and innovative ways to organize and capture our lives, but how much trust can we put in our mobile devices?
Is it possible to hack my iPhone?
Since 2006, Apple have all but outright claimed their products to be ‘completely unhackable’. They even went as far as to launch a somewhat tongue-in-cheek ad campaign comparing the superior security of their products to Microsoft Windows.
While it’s great that Apple is taking security seriously and seems to mostly do a great job of protecting the users in their ecosystem, this ‘unhackability’ myth has cultivated a level of complacency amongst many Apple users.
This is particularly true for iPhone users, many of whom don’t even consider the security of their device any further than a password, Touch ID or Face ID. And while for most people that will suffice, it won’t stop an attack from a hacker determined to peek into your private data.
Think your iPhone is hacked?
Quickly and easily check your iPhone for spyware today with the award-winning Certo AntiSpy.
Let’s get one thing clear – it’s very possible for your iPhone to be hacked. Here’s how:
1. Commercial Spyware
Believe it or not, there are software programs commercially available that can be used to hack an iOS device.
Additionally, they are anything but expensive. These applications can cost as little as $30 for one month of tracking using basic features (advanced features are more costly – but still not unaffordable for most people).
We’re not naming the software here, but to give you a better idea of what you’re up against, this type of commercial software can:
- Turn on microphone & listen in on live calls
- Track real-time location
- View private photos & videos
- Log keystrokes to detect passwords and usernames, etc.
- Be 100% invisible to the victim
- Provide remote updates (meaning whoever is spying on you can check on you no matter where in the world they are).
It’s quite simple to install. That means anyone could do it. All the hacker would need is access to your device and about 2 minutes to install it.
Note: There are certain limitations to this type of software (such as the hacker will normally need to Jailbreak your phone first), but even then, it would be possible for a hacker to collect a plethora of personal information in just a very short amount of time.
2. Tracking Apps
These types of apps are similar to the software mentioned above, except for the fact that they are much more widely available. They tend to pose as more ‘family friendly’ apps designed to help parents keep track of their kids – which is fine, if not a little overbearing. But these apps can also be misused by hackers who just want to keep track of where you go and what you do.
Most people don’t know this, but these apps can be downloaded directly from the Apple App Store.
Compared to the commercial software listed above, these apps are less than a third of the price per month! This makes them even more accessible and more likely that someone would be tempted to install them onto your device.
3. Keyloggers
Keyloggers are a fairly new method of hacking an iPhone, but one that is growing in popularity. They are often offered by spyware makers as an alternative to full spyware apps which can be harder to install.
While a keylogger does not give the hacker access to everything on the device, it is much easier to get onto an iPhone and could go unnoticed for months.
Once installed on an iPhone, a keylogger will silently pass everything you type onto a hacker. This could include your private messages, the websites you visit and, more worryingly, the passwords to your online accounts or social media.
4. iCloud
This one is a lot less common than the above two methods, but sometimes the only thing a hacker needs is access to your iCloud account details. There are various methods of obtaining these details, but once they have them, they can then access any of the personal data on your iCloud account.
That means photos, messages, contacts and more – essentially any data from your phone that is uploaded to iCloud. There are even companies that offer this as a service for as little as $30, giving the hacker access to all information from a hacked account in a nicely presented online report.
Once they have that information it can be used for a wide range of purposes. It really depends on who is hacking you and why.
4. Enterprise Apps
One way that hackers try to circumvent Apple’s security protocol is to install what is known as an ‘enterprise app’. This is usually reserved for cases where a company might want a bespoke app installed onto employee’s devices, without having to distribute their app to the entire world via the App Store.
However, hackers have learned that this is an effective way of getting malicious software onto a device and gaining access to a wealth of private user information. See Number 2 in this article for more information.
Compared to the methods mentioned above, this is quite a complicated way of doing things and requires substantially more technical knowledge to implement, although it’s not outside the ability of most tech-savvy people.
5. WiFi Hacking
While it’s extremely difficult to infect an iPhone with malware over WiFi, it’s still possible for a hacker to intercept data if you’re connected to an insecure or compromised network.
Whenever we connect to public WiFi we are at risk of falling victim to a hacker. Public WiFi is notorious for being less secure than the WiFi in most people’s homes.
The biggest risk comes from when you are accessing a public network that isn’t properly encrypted against attacks. For example, it doesn’t require a password to log onto the network, or the router/modem isn’t properly protected (and they still have the default passwords).
An insecurely configured network allows more opportunity for experienced hackers to jump onto the network and act as a ‘man-in-the-middle’, meaning they can either intercept network data or funnel all network traffic through their own system and collect users’ personal data along the way.
Award-winning spyware detection
Millions trust Certo to protect their mobile devices from hackers. Find out how Certo AntiSpy could help secure your iPhone.
How can I protect my iPhone from being hacked?
There are steps that you can take to protect your iPhone from hackers and spyware technology:
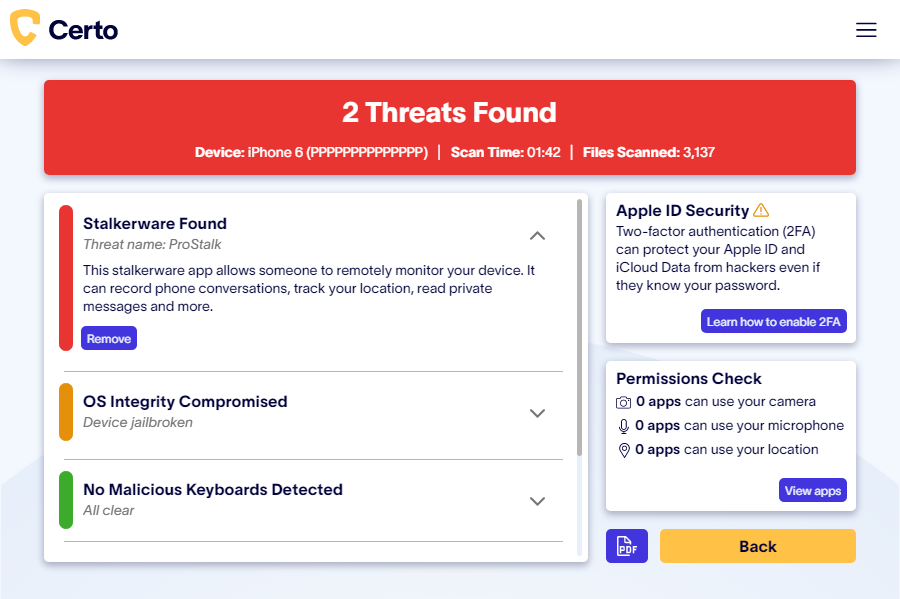
- Use Certo AntiSpy – If you suspect your iPhone has been hacked then you should run a malware scan as soon as possible. Certo AntiSpy can perform a thorough scan of your device and allow you to quickly and easily remove any threats detected. Download it here.
- Never jailbreak your iPhone – Jailbreaking your iPhone leaves your device much more vulnerable to hacking attacks. Leaked documents from an Italian security firm ‘Hacking Team’, who sell tools to hack phones, revealed they had multiple methods to hack jailbroken iPhones, but none to hack iPhones that were not jailbroken.
- Keep your device up to date – Keep your iPhone and all your apps updated, this ensures you have the most up-to-date protection for your data and information. You can set both your device and apps to auto-update, which makes things even easier.
- A strong and secure password – The most important password you can use for your device is the one at the main lock screen. Alongside Touch ID and Face ID this is your best defense against a hacker gaining physical access to your device. The best advice here is to use the option for a longer alpha-numeric password as opposed to a simple, 4-digit password.
Even worse is using a simple password such as “1111” or “1234”!
- Two-Factor authentication – Enabling two-factor authentication provides an extra layer of security, because even if a hacker knows the password to your iCloud account, they would still need physical control of your device in order to gain entry. This helps to ensure that you are the only person who can access your account.
- Only sync whats necessary – The more data you sync with iCloud, the more of your private data is stored online and could potentially be accessed by a hacker. Think carefully about what data you are syncing and if you don’t need to store a copy of it in iCloud, consider turning off syncing for that data type.
Bonus Tip: Turn on Advanced Data Protection in your iCloud settings to enable end-to-end encryption for all data you sync with iCloud, meaning that hackers won’t be able to access any of your data even if they manage to break into your iCloud account.
- Disable auto-join to known Wi-Fi networks – By default, Apple configures their iPhones to automatically connect and share your data with known Wi-Fi networks. A hacker can configure their malicious Wi-Fi network to disguise itself as a known network and automatically connect to your iPhone and steal your data. To prevent this, switch off auto-join in settings and only connect to trusted Wi-Fi networks.
- Disable Wi-Fi Sync – This allows your iPhone to automatically backup to a computer on the same Wi-Fi network. Some spyware providers exploit this feature to allow a nosey partner to access the data from this backup and therefore view their victim’s photos, messages, call logs and much more. Use our free tool to check if WiFi Sync is enabled on your iPhone and turn it off with one click.
Wrapping up
While Apple products have a reputation for being highly secure, it is important to acknowledge that they are not completely unhackable. As technology continues to advance, new methods of hacking iPhones will inevitably arise, and it is essential for users to stay vigilant in protecting their personal information.
To minimize the risk of being hacked, it is recommended that iPhone users keep their software up to date, avoid jailbreaking their devices, and use strong passwords, Touch ID, or Face ID. Additionally, being cautious about downloading third-party apps and connecting to unsecured WiFi networks can also help reduce the risk of being hacked.
It is also important to remember that if you suspect your iPhone has been hacked, there are tools available to help you detect and remove any spyware or malicious software. Taking steps to protect your device and personal information can go a long way in ensuring the security of your digital life.