Can Someone Hack My Phone From My Number?

Updated:

Many people believe that a phone can be hacked just by knowing its number, meaning that all of your private data is available to hackers without them ever needing to touch your device.
It’s alarming to think that if someone wanted to hack your cell phone, all they would need was your number. You’d be forgiven for thinking this is a very real threat to your mobile security. But is this actually the case or is it just a myth? In this blog we examine the facts and discuss what is and isn’t possible when it comes to phone hacking.
Think your phone is hacked?
Quickly and easily run a spyware check on your cell phone today with one of our award-winning apps.
Is It True That Someone Could Hack Your Phone with Just Your Number?
Quite simply — no, it isn’t. But you could be forgiven for thinking that it is. If you’ve ever done an online search to find out whether someone can hack your mobile device with just your phone number, you might have come across several articles and blog posts claiming that it’s possible.
However, most of the search results for this query use the discussion to promote and sell spy software that actually requires physical access to the victim’s device. This type of software is also commonly referred to as “monitoring software” but is really just a thin veil for what is widely known as spyware.
Let’s look at an example from a search using the keyword “is it possible to hack someone’s cell phone number?”
At the beginning of this article, they claim that it’s easy to hack a phone with just its number. However, as you read on it becomes clear that the goal of the article is to promote a spy software tool that does not really work just by knowing someone’s cell phone number.
If you look closely at any article claiming that a cell phone can be hacked just by knowing its number, you’ll find that they all have one thing in common: promotion of a spyware tool that requires more than just the number to install it, such as physical access to the device or iCloud login details.
While these spyware tools can certainly cause extreme harm and essentially steal all of the sensitive information on your device, fortunately the claim that they can be installed with just a number is false.
What Can a Hacker Do with My Phone Number?

That said, there are a few ways a hacker can use your phone number to gain access to your device as part of a larger attack:
- ‘Phishing’ for personal data. It’s common for hackers to send fake text messages to their targets in order to gain username and password information (this is known as phishing). The text will typically contain a malicious link to a fake website that will look almost identical to the legitimate version. The fake version will record any entered data and send it back to the hacker.
- Sending links to malicious apps. One of the ways that hackers will try to hack devices is by sending links to malicious apps via text messages. The hacker might be posing as a legitimate company providing a seemingly genuine app (photo editors and fitness trackers are common examples). The aim is to get you to install the app onto your device, allowing the hacker to gain access to your data without your knowledge.
- Two-factor authentication. This is when a company will confirm your identity by sending you an SMS code to input when logging into your account. A hacker could retrieve this code and gain access to your account if they have cloned your SIM card or have spyware installed on your device.
- Sending text messages from your number. If a bad actor knows your cell phone number and wants to cause havoc, they could easily send a message pretending to be you. Many cheap online services exist that allow someone to send a text message from any number they choose. All they need to know is the sender’s number.
- Determining your carrier and the country you are currently in. There are some paid online services where you can enter a phone number and it will tell you the carrier (e.g., Verizon) and the country where the mobile device is currently located. This can provide some limited, but often useful, information to a potential hacker.
It’s important to reiterate that it’s not possible for someone to simply type your number into some form of malicious software and click “Hack.” There is usually a process of convincing you to reveal personal information voluntarily or downloading a malicious app onto your phone.
Need to check for phone hacking?
Certo's award-winning spyware detection tools for iPhone and Android are trusted by millions worldwide.
The Real Ways Your Phone Can Be Hacked
Although it’s not possible for someone to hack your phone with just your number, there are some other methods they might use. Below we’ve listed the common types of hacking, along with ways to easily protect yourself.
iOS hacking
Apple devices are usually harder for hackers to infiltrate than Android devices. This is due to Apple’s tougher security measures. However, there are a few ways that hackers can steal data from your iOS device.
Firstly, they could compromise your iCloud account without needing physical access to your device. If a hacker is able to break into your account, they can access any data that you have synced from your iPhone. This could include contacts, chat and messaging history, photos, and more.
Secondly, spyware can be installed onto an iOS device, but this requires the hacker to get hold of the device for a few minutes in order to bypass Apple’s security. If they succeed, they will have access to everything on your device, be able to track your location and may even be able to monitor you via the microphone and cameras.
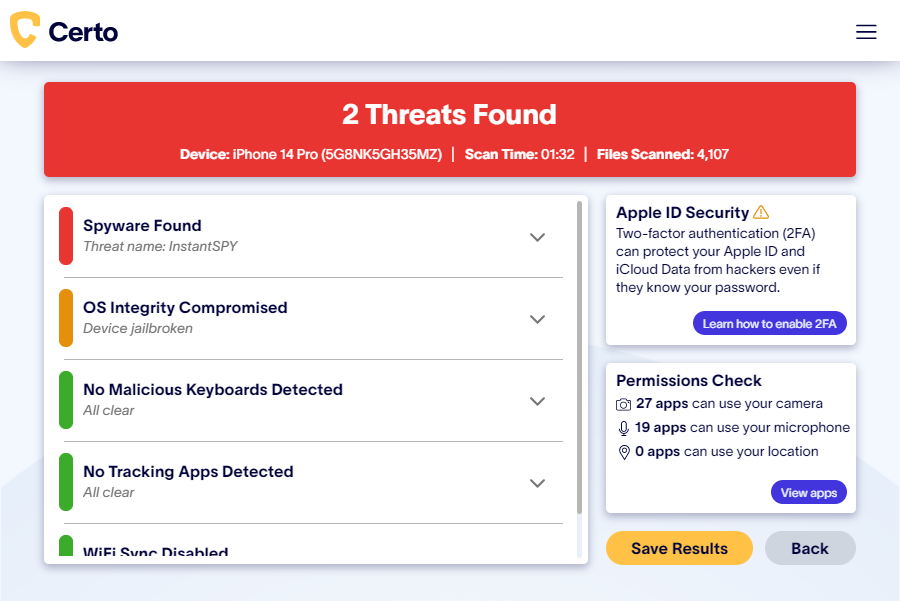
The best way to protect yourself from someone installing spyware onto your iPhone is to scan your device regularly. Unfortunately, iPhone apps can’t do this as they are unable to access areas of the device where spyware typically hides. But you can easily run a full scan of your iPhone if you have access to a computer.
Certo AntiSpy makes it extremely easy to check your device to see if there is spyware installed. This industry-leading software is the best defense against spyware for Apple mobile devices.
Android hacking
Android devices can offer more opportunities for hackers, since their system is much more open to control by the user. This means that it’s easier for a hacker to find ways to exploit this system.
By far the most common way of hacking an Android phone is by using spyware. This software can be purchased for as little as $30 and can be easily installed directly onto the device with little to no actual “hacking” required.
It’s also possible to hide this spyware from the victim, so you could be using your cell phone as normal, completely unaware of the fact that someone is remotely monitoring your actions, stealing your data and potentially even watching you via the device cameras.
Unlike Apple devices, there are several Android apps available that can perform a complete scan of the device for spyware. We recommend Certo Mobile Security, which can be downloaded for free from the Google Play Store.
The app will let you check whether there is any spyware installed on your device with just a simple tap. Any spyware that is installed onto the device can then be easily removed.

Summary
Hopefully this has helped to reassure you that it is not possible for someone to hack your phone with just your number. However, phone hacking is a real threat and there are many other ways for hackers to gain access.
Install Certo for Android or iPhone today and reduce the risk of phone hacking. Certo will scan your device for potential threats and help you to quickly and easily remove them, securing your data and giving you peace of mind.
Cover Image by DC Studio on Freepik