60,000 Phones Infected with Spyhide Stalkerware

Published:

Recent research has uncovered unsettling data that exposes a clandestine phone surveillance application, Spyhide, actively gathering confidential data from a multitude of Android devices globally.
Spyhide is an insidious form of stalkerware, or spouseware, typically installed on a target’s device by someone privy to their passcode. The app is skillfully concealed on the device’s home screen, making detection and removal exceedingly difficult. Once installed, Spyhide surreptitiously and continuously harvests data including contacts, messages, photos, call logs and recordings, and real-time precise location.
Check your phone for Spyhide
Download Certo's free Android app and quickly check if Spyhide is lurking on your device and remove it with a tap of a button.
Despite their cunning tactics and extensive access to a victim’s phone data, these stalkerware apps have a notorious reputation for being prone to glitches. They can inadvertently expose, leak or further compromise the stolen private data, amplifying the potential risks posed by such phone surveillance apps. Currently, Spyhide has joined the ranks of such malicious operations.
A Switzerland-based hacker, Maia arson crimew, shared in a blog post that they exposed a part of the spyware’s development environment. This allowed them access to the source code of the web dashboard that abusers use to peruse the stolen data from their victims. Exploiting a flaw in the dashboard’s poorly written code, crimew was able to access back-end databases, revealing the covert spyware operation and its probable administrators.
Crimew submitted a text-only copy of Spyhide’s database to TechCrunch for verification and scrutiny.
Detailed records from about 60,000 compromised Android devices, ranging from 2016 to mid-July this year, were stored in Spyhide’s database. These records comprise call logs, text messages, and precise location histories stretching back years. Furthermore, it also includes information on each file, such as timestamps for photos or videos and durations of recorded calls.
TechCrunch processed almost two million location data points using offline mapping software to visualize and comprehend the global extent of the spyware.
The findings revealed that Spyhide’s surveillance network envelops every continent, with significant victim concentrations in Europe and Brazil. There are more than 3,100 breached devices in the U.S., a mere fraction of the total number worldwide, yet these victims are among the most heavily surveilled based on the volume of location data alone. In one instance, a U.S. device infected by Spyhide silently uploaded more than 100,000 location data points.
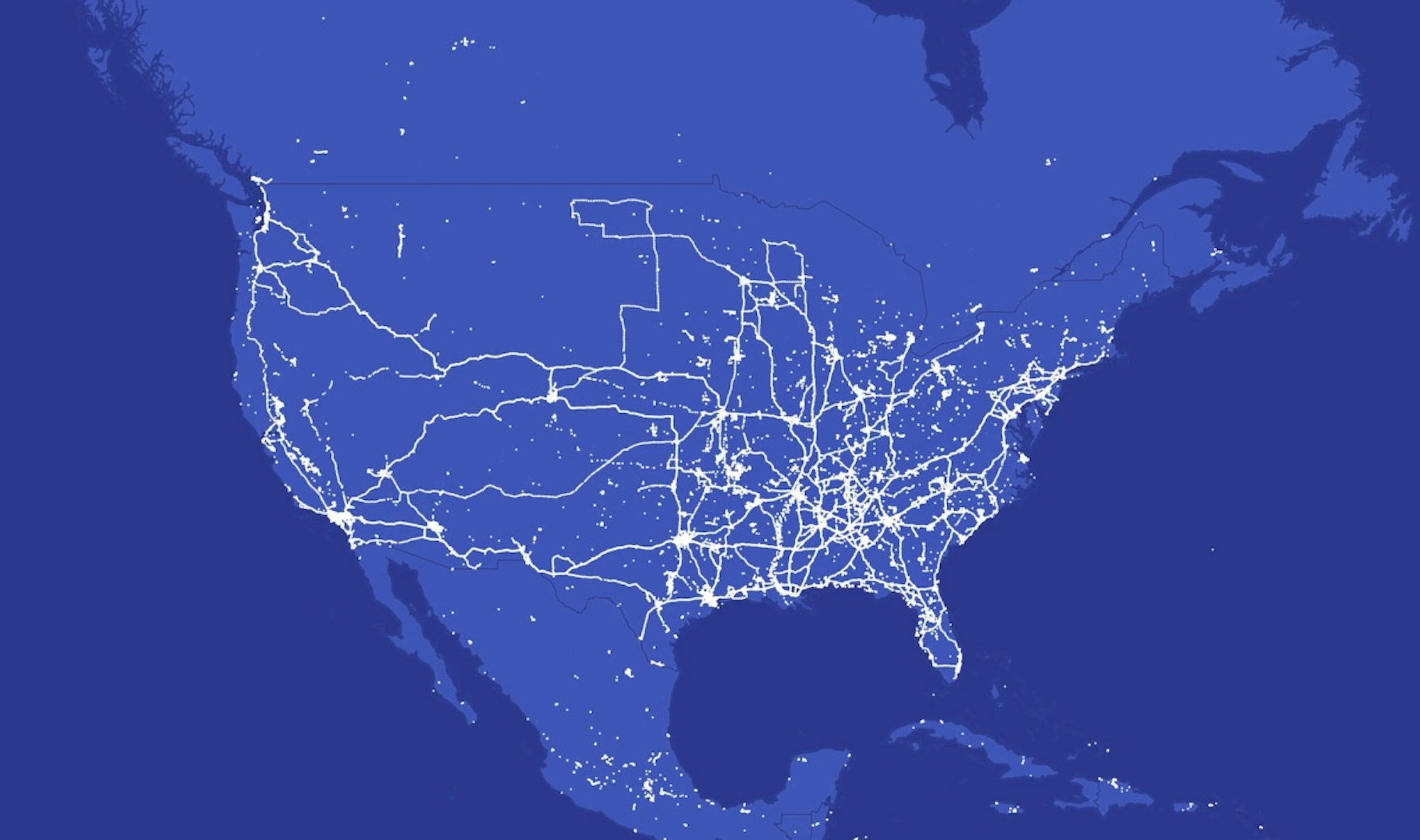
Image Credit: TechCrunch
Spyhide’s database also held records of approximately 750,000 users who had registered with the intention of planting the spyware app on a target device.
Despite the alarmingly high user registration, the majority did not proceed to compromise a phone or purchase the spyware, as per the records. However, Tech Crunch’s analysis found that more than 4,000 users had control over more than one breached device. A smaller number of user accounts had control over several dozens of compromised devices.
The data contained 3.29 million text messages with private information like two-factor codes and password reset links; over 1.2 million call logs with the receiver’s phone numbers and call duration, and about 312,000 recorded call files; more than 925,000 contact lists with names and phone numbers; and 382,000 photos and images. The data also included records of nearly 6,000 ambient recordings secretly captured from the victim’s phone microphone.
Spyhide, allegedly developed in Iran and hosted in Germany, provides no information about its operators on its website. However, the source code revealed the names of two Iranian developers profiting from the operation. These developers did not respond to multiple requests for comment.
Apps like Spyhide, that endorse covert spousal surveillance, are prohibited on Google’s Play Store. As such, users must download the spyware directly from Spyhide’s website. TechCrunch, using a virtual device and a network traffic analysis tool, found that the app sends the harvested data to a server hosted by the German web hosting giant, Hetzner.
Upon contacting Hetzner, spokesperson Christian Fitz informed TechCrunch that hosting spyware is not permitted. Following this report, Spyhide’s domain became inaccessible.
How can I check if I’m affected?
For Android users concerned about this new spyware, Certo Software recommends downloading and installing the free Certo Mobile Security app. This app can detect the presence of Spyhide on your device and allows you to uninstall it with a single tap.