How To Find Out Who Hacked Your Phone

Updated:

Nowadays, it’s extremely important to pay attention to your mobile security. Just imagine if all the data stored on your mobile device was suddenly available to an anonymous hacker who has managed to break into your phone.
That means every website you’ve visited, every picture you’ve taken, every password you’ve entered—it could all be accessed by hackers. Not to mention the possibility of fraud or identity theft once the hacker gains access to your personal and financial information.
If you know or suspect that your phone has been hacked, there are a few things you can do to regain control. Read on to find out who hacked your phone, and how to stop them in their tracks.
In this article, we explore ways to detect malicious activity, find out who hacked your phone, and identify the steps you can take to prevent and remove any threats.
Think your phone is hacked?
Quickly and easily run a spyware check on your cell phone today with one of our award-winning apps.
How Do I Know If My Phone Has Been Hacked?
There are a few warning signs that might lead you to think that your phone is hacked. Let’s cover these now:
1. High battery temperature
If you’ve noticed that your phone is a lot warmer than usual, this is potentially a sign of hacking. Because intruders usually use software on your device to help them track all of your data, this requires your device’s processor to work harder, in turn generating more heat. Which leads us to our next point…
2. Battery draining faster than usual
Again, if a hacker has installed malicious software onto your device it will require more processing power to run. This will inevitably cause your phone battery to drain a lot faster than usual, and poor battery life could be an indicator that your phone is hacked.
It’s important to note that although high battery temperature and fast battery drain can be a sign of phone hacking, there may be other explanations. For example, phones are usually hotter when running resource-heavy apps (e.g. Games), and battery life deteriorates as phones get older.
3. Background noise
If you’re hearing background noises coming from your phone such as echoes, static, or clicking sounds, this may be a hint that your phone is hacked. Background noise like this is usually most audible when you’re on phone calls and is a potential sign that someone is listening in. So, it’s probably a good idea to not share anything too personal if it sounds like R2-D2 is on the other end of the line.
4. Pop-ups or changes to your screen
Malware can also be responsible for suspicious pop-ups or changes to your home screen or apps. Any significant changes you don’t remember making are a warning sign that your cell phone has been hacked.
Have you experienced weird appointments or reminders in your phone’s calendar app? This is likely the result of phishing. This is when hackers gain access to your personal and business calendars in order to steal information.
5. Distortion (similar to when you are on a call)
If you’ve ever used your phone near another electronic device (such as a TV) and noticed a distortion in the audio, even though you aren’t on a phone call, this might be a symptom that someone has hacked your device or perhaps even installed hardware (a physical component) onto your phone.
6. Presence of suspicious apps

A hacker may install spy apps on your device, which are designed to monitor your activity. These apps run in the background and unlike traditional apps, they don’t show a visible icon on your screen.
You may be able to identify any suspicious apps by looking at your active hours, battery usage, memory, and data usage. However, it’s normal for cell phones to have a number of hidden system apps that you don’t know anything about, making it hard to distinguish between what is needed for your phone to run, and anything that may be monitoring your activity.
7. Certo has detected spyware on your phone
If you think that your phone is hacked, you should download Certo to find out if your suspicions are correct. After installing Certo Mobile Security for Android or Certo AntiSpy for iPhone, you can scan your device for potential threats. If anything suspicious is identified, Certo will help you to remove it.

Uncover mobile spyware with Certo
Certo's award-winning spyware detection tools for iPhone and Android are trusted by millions worldwide.
Who Can Hack My Phone?
Once you know that your phone has been hacked, the next step is to discover who did it. Is it an anonymous third party? Or even more worrying, is it someone you know?
A common misconception is that hacking a phone requires some mysterious computing superpowers. However, today this is far from the truth.
Spyware is available on the market for as little as $30 and does not require any specialist knowledge to use. All the hacker needs is access to your phone for just a few minutes to install the spyware and start monitoring your activity.
Professional hackers are even able to steal your data without physical access to your phone, and there are thousands of people working in black market operations trying to find a way to hack cell phones in order to obtain sensitive data.

How to Trace a Phone Hacker: Who Is Spying on My Phone?
If you suspect that your phone is hacked, there are a few things you need to do. Here are three methods of tracing a phone hacker:
1. Find out who has installed spyware on your phone
Spyware is malicious software designed to track everything you do on your device. A common method of installing spyware is for someone to plant a hidden spy app on your phone. This is most likely to happen if someone has physical access to your device, even if it’s just for a short while. It could also happen (although it’s less likely) if you click on a suspicious link and download malware disguised as an innocent app.
Spyware is often invisible to you as the device owner, and could potentially give the attacker full access to your data. Additionally, most spy apps are designed to protect the identity of the hacker who installed them.
They work by sending captured information to the spyware provider, rather than directly to the hacker. The hacker then logs into the spyware provider’s website to retrieve information stolen from the infected device. This means details of who installed the spyware are not stored anywhere on the infected device, giving the hacker a layer of anonymity. This can make finding out who installed spyware on your phone somewhat difficult.
A great way to combat this is to use Certo AntiSpy (for iPhone) or Certo Mobile Security (for Android). Certo’s anti-malware apps will help identify the name of the spyware that is installed on your phone, allowing you to track down the manufacturer of the spy software. You can then inform them that someone has installed the software without your permission and request details of the person who originally purchased the software license.
Here is a sample email you can send to the software developer in order to get the required information:
Dear Sir/Madam,
I have performed a malware scan on my phone and found that <spyware name> is installed on my device. I did not authorize for this software to be installed on my phone and it has been done so completely without my permission.
I therefore need to find out who installed this spyware on my device, so please can you provide this information as soon as possible? My phone number is <phone number> and my device serial number is <serial number>.
I trust this is all the information you require to retrieve the information from your systems, but please let me know if you need anything else to do this.
Yours faithfully
John Doe
Scan your phone for spyware with Certo
Certo helps you to identify and remove spyware and malware from your device.
2. Find out who hacked your iCloud account (iOS devices only)
iCloud is a great solution for backing up your Apple device and keeping photos, contacts, and other data stored in the cloud. You can save everything from custom app settings and text messages to videos you’ve taken with your phone.
Unfortunately, as good as Apple claims its security to be, there are still ways for a hacker to break into your account.
The main difference between having your phone hacked and your iCloud account hacked is that intruders don’t need to install any software on your phone to access your iCloud account.
A different method of investigation is required to find out who has hacked your iCloud account. Firstly, you will need to contact Apple and ask them to provide you with all the details of recent access to your account. This will usually include IP addresses that can be used to identify the hacker.
Look out for email notifications from Apple that alert you to new account logins. Immediately report suspicious activity directly to Apple.
You can view a more in-depth explanation of this type of hack here.
3. Setting a trap for a hacker
Another method you can use is to booby-trap your phone if you suspect that someone might want to infiltrate. This doesn’t guarantee protection from them installing anything onto your phone or viewing your information, but it will help you catch them red-handed or can act as a deterrent—much the same as a home alarm system.
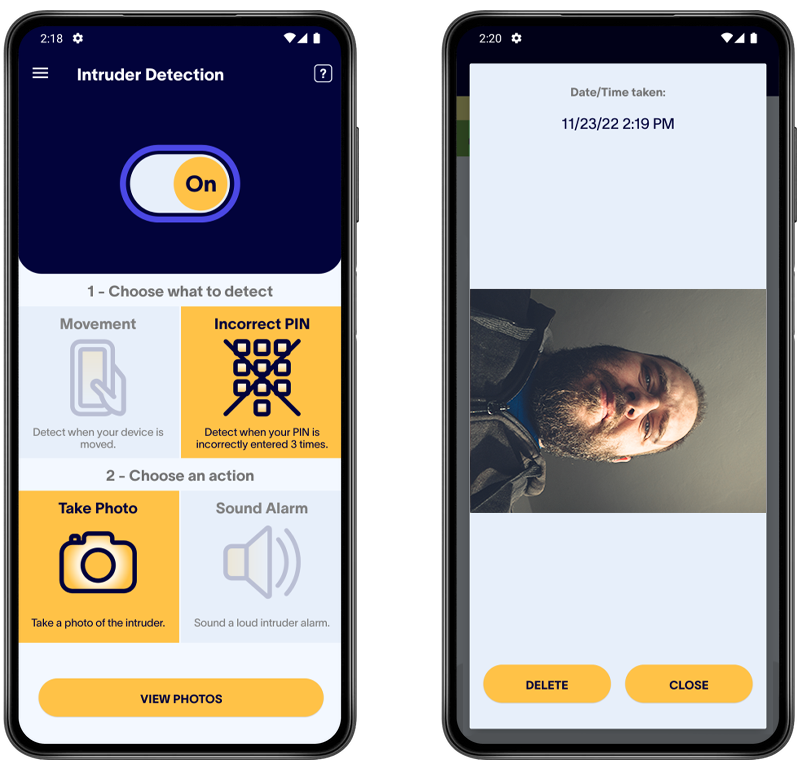
The Certo Mobile Security app for Android allows users to take a silent photo of anyone who might be trying to hack their phone. Along with an alarm, this feature can be set up to trigger whenever someone moves your phone or enters an incorrect password multiple times. This feature is also coming to Certo Mobile Security for iOS in the near future.
What Should I Do If I Suspect My Phone Has Been Hacked?
1. Run a spyware scan immediately
Certo has the ability to instantly scan your phone and inform you of any potential threats it finds on your device. If spyware is detected then you can refer to the information above to find out exactly who hacked your phone.
2. Take steps to remove those threats
This is easy with Certo’s apps for iPhone and Android. Once a threat is identified, you can safely remove it from your device with the tap of a button.
Whether you’re an Apple or Android user, it’s also a good idea to keep your operating system updated. This makes it harder for hackers to exploit security vulnerabilities and access your data.
You could also try to remove threats from your phone by performing a factory reset, but this is a last resort and should only be carried out after you have backed up all your data to an external device or to cloud storage.
3. Change your passwords
This is a very important step. You should change your passwords as soon as possible to prevent anyone from gaining unauthorized access to your private accounts. Make sure to create complex passwords, ideally with a combination of upper and lowercase letters, numbers, and symbols.
How to Protect Yourself Against Future Attacks
In today’s hyper-connected world, phone hacking is a serious threat that can negatively affect your personal life, your finances, and more. Luckily there are a few things you can do to reduce the risk of it happening to you and to block hackers from accessing your device.
1. Use Certo
Perform regular device scans with Certo’s apps for iPhone or Android. This allows you to quickly find and remove any malware that has infected your phone and gives you the tools to keep your device and personal data secure.
2. Use a Virtual Private Network (VPN)
Virtual private networks encrypt all of the data that you share online so that no one is able to access it. Whether it’s your email inbox, social media accounts, passwords, or browsing history, VPNs make it much harder for hackers to access your sensitive data. Make sure you research different VPN providers carefully before signing up to find a safe and secure option.
3. Be wary of public Wi-Fi
Public Wi-Fi connections are those which are “open” and don’t ask you for a password to access them. You might get an option to connect to them if you’re in a shopping mall, a park, or another public place.
However, you should be wary of any personal information you share online using public Wi-Fi. This type of connection is much easier for hackers to gain access to than secured Wi-Fi connections that require a password.
If you do need to be online when you’re out and about, we recommend using your mobile data or a VPN like NordVPN to reduce the risk of phone hacking.
4. Use two-factor authentication
Two-factor authentication is a great way to protect your phone from hackers. It works by requesting two different types of authentication when you log in to an online account—for example, your iCloud account.
To log in, you might be required to enter your Apple ID and password, as well as a verification code sent to you by text message.
The extra information required makes it much more difficult for hackers to gain access to your private data.
Key Takeaways
Today spyware is easy to buy and install, making it possible for almost anyone to hack your phone. There are a few things you can do to trace a hacker and reduce the risk of phone hacking:
- Finding the name and type of the malware present on your phone is the first step to finding out who has hacked your device.
- Choose strong passwords and change them regularly. Don’t use the same password for everything, and don’t share your passwords with anyone.
- Use two-factor authentication to make it harder for hackers to gain access.
- Install Certo Mobile Security for Android or Certo AntiSpy for iPhone to protect your phone against security threats.
Award-winning mobile security
Certo's industry-leading spyware detection tools for iPhone and Android are trusted by millions worldwide.